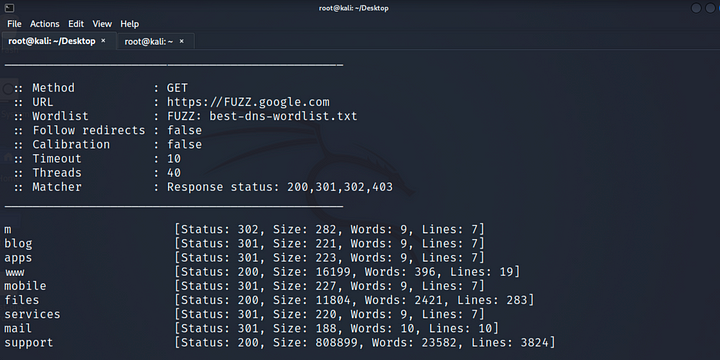
Active Subdomain Enumeration Using FFUF

Active Subdomain Enumeration Using FFUF

Favicon hash detecting using FavFreak
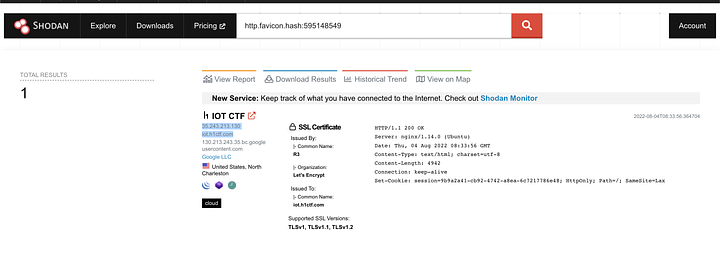
Using shodan Search Engine to detect site that have same favicon hashed

use a nrich tool to check out the subdomains
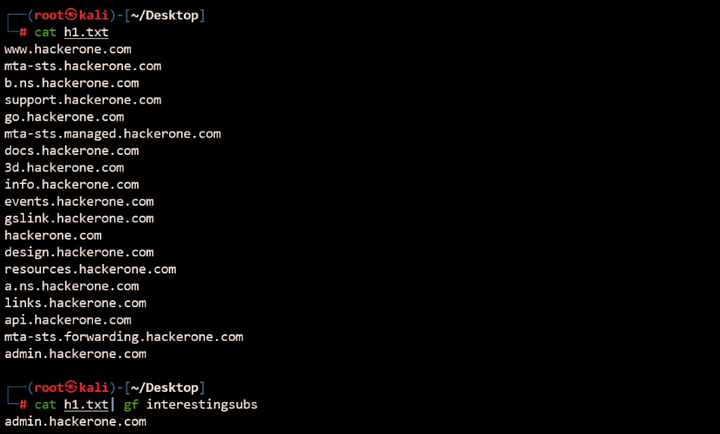
gf interestingsubs pattern list to find interesting subdomains
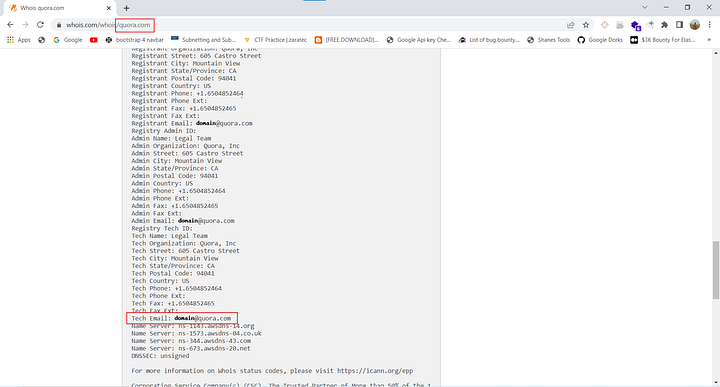
Performing whoislookup on target domain
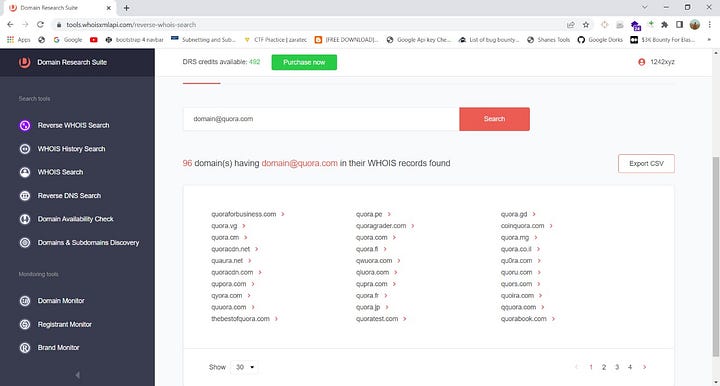
Searching For Tech Emails

uncover tool link https://github.com/projectdiscovery/uncover

File List Created for the host xyz.com with request and response

Finding open ports and service running using naabu